comptia CS0-003 Exam Questions
Questions for the CS0-003 were updated on : Apr 18 ,2025
Page 1 out of 15. Viewing questions 1-10 out of 149
Question 1
A recent audit of the vulnerability management program outlined the finding for increased awareness of secure coding practices. Which of the following would be best to address the finding?
- A. Establish quarterly SDLC training on the top vulnerabilities for developers
- B. Conduct a yearly inspection of the code repositories and provide the report to management.
- C. Hire an external penetration test of the network
- D. Deploy more vulnerability scanners for increased coverage
Answer:
a
Question 2
An analyst is reviewing a vulnerability report for a server environment with the following entries: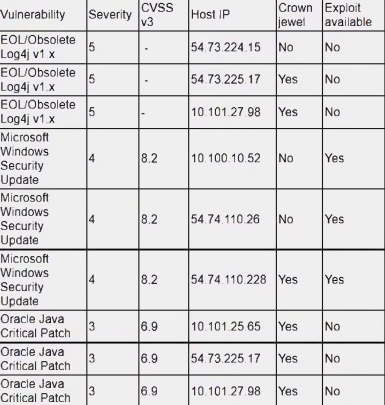
Which of the following systems should be prioritized for patching first?
- A. 10.101.27.98
- B. 54.73.225.17
- C. 54.74.110.26
- D. 54.74.110.228
Answer:
d
Question 3
The analyst reviews the following endpoint log entry: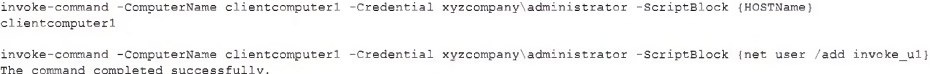
Which of the following has occurred?
- A. Registry change
- B. Rename computer
- C. New account introduced
- D. Privilege escalation
Answer:
c
Question 4
A security analyst is reviewing a packet capture in Wireshark that contains an FTP session from a potentially compromised machine. The analyst sets the following display filter: ftp. The analyst can see there are several RETR requests with 226 Transfer complete responses, but the packet list pane is not showing the packets containing the file transfer itself. Which of the following can the analyst perform to see the entire contents of the downloaded files?
- A. Change the display filter to ftp.active.port
- B. Change the display filter to tcp.port==20
- C. Change the display filter to ftp-data and follow the TCP streams
- D. Navigate to the File menu and select FTP from the Export objects option
Answer:
c
Question 5
After completing a review of network activity, the threat hunting team discovers a device on the network that sends an outbound email via a mail client to a non-company email address daily at 10:00 p.m. Which of the following is potentially occurring?
- A. Irregular peer-to-peer communication
- B. Rogue device on the network
- C. Abnormal OS process behavior
- D. Data exfiltration
Answer:
d
Question 6
A systems administrator is reviewing after-hours traffic flows from data-center servers and sees regular outgoing HTTPS connections from one of the servers to a public IP address. The server should not be making outgoing connections after hours. Looking closer, the administrator sees this traffic pattern around the clock during work hours as well. Which of the following is the most likely explanation?
- A. C2 beaconing activity
- B. Data exfiltration
- C. Anomalous activity on unexpected ports
- D. Network host IP address scanning
- E. A rogue network device
Answer:
a
Question 7
Which of the following would a security analyst most likely use to compare TTPs between different known adversaries of an organization?
- A. MITRE ATT&CK
- B. Cyber Kill Cham
- C. OWASP
- D. STIX/TAXII
Answer:
a
Question 8
After conducting a cybersecurity risk assessment for a new software request, a Chief Information Security Officer (CISO) decided the risk score would be too high. The CISO refused the software request. Which of the following risk management principles did the CISO select?
- A. Avoid
- B. Transfer
- C. Accept
- D. Mitigate
Answer:
a
Question 9
Which of the following actions would an analyst most likely perform after an incident has been investigated?
- A. Risk assessment
- B. Root cause analysis
- C. Incident response plan
- D. Tabletop exercise
Answer:
b
Question 10
An incident response team found IoCs in a critical server. The team needs to isolate and collect technical evidence for further investigation. Which of the following pieces of data should be collected first in order to preserve sensitive information before isolating the server?
- A. Hard disk
- B. Primary boot partition
- C. Malicious files
- D. Routing table
- E. Static IP address
Answer:
c